Let's talk about AWS VPC endpoints
Natalia discusses AWS VPC endpoints, specifically the differences between Gateway and Interface endpoints.

VPC endpoints enable us to establish private connections between your VPC and supported AWS services, bypassing the need for public internet access, making your infrastructure more secure and improving data protection. In this blog post, we will look into AWS VPC endpoints, specifically focusing on differences between Gateway and Interface endpoints, and explore why it is important to consider them in the context of AWS infrastructure.
Gateway Endpoints
First lets talk about Gateway Endpoints, which are available to connect to S3 and DynamoDB. We would use them if we require connectivity from within AWS network, without having to create internet gateway, NAT device, or VPN. Unlike Interface Endpoints, they do not use AWS PrivateLink, are free of charge and are available only in the Region where you created it.
In a Gateway Endpoint, traffic is routed from your VPC, via the Gateway Endpoint, to S3 or DynamoDB. It serves as a target for a route in your route table for traffic destined for one of these services.
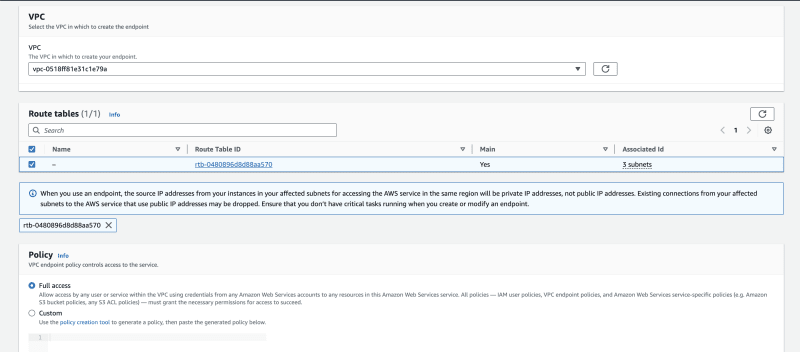
When creating a Gateway Endpoint first you will have to select route table in which to create routes to the service and add resource policy - you can select full access to allow all operations by principals, or create a custom policy to enable more granular access, for instance restricting which S3 buckets can be accessed via the gateway endpoint.
Note that Gateway Interfaces do not allow access from on-premises networks, peered VPCs in other AWS Regions, or through a transit gateway - in those instances you will have to use Interface Endpoints.
Interface Endpoints
Interface Endpoints utilise AWS PrivateLink, that securely connects your VPC to supported AWS services, such as EC2 API, ECS, Secret Manager, Lambda, but also services hosted by other AWS customers, AWS Partner Network (APN) partners in their own VPCs, or allows access from on premises. This is done by creating elastic network interfaces (ENIs) within your VPC that serve as the entry point for traffic destined to these AWS services.
The key difference between Interface and Gateway Endpoints lies in their underlying architecture, cost and usage. While Gateway Endpoints are limited to S3 and DynamoDB and are free of charge, Interface Endpoints support a broader range of services but incur a cost based on the amount of data processed.
When we create an Interface Endpoint, it gets associated with a specific subnet in our VPC and creates an ENI. This ENI is assigned a private IP address from the subnet's IP range. Your VPC traffic to the AWS service then goes through this private IP address, ensuring that the data never goes over the public internet. This setup enhances security and could potentially reduce data transfer costs.
Use Cases of Interface Endpoints for AWS Services
Interface Endpoints are particularly beneficial for secure and private access to AWS services not supported by Gateway Endpoints. For services like Kinesis or Lambda, and when latency and secure data transfer are crucial, Interface Endpoints can provide a consistent, low-latency connection, vital for real-time data processing and serverless computing scenarios.
Next, using AWS Secrets Manager integrated with Interface Endpoints allows you to access Secrets Manager within your VPC without exposing the traffic to the public internet. This would be crucial for applications that need to securely access sensitive information, like database credentials or API keys.
Last example use-case I want to discuss is ECS, which can also be used with Interface Endpoints for secure, private communication with other AWS services. For example, an ECS cluster in a VPC can privately pull images from Amazon Elastic Container Registry (ECR) or securely store logs in CloudWatch, essential for compliance-sensitive applications.
These are just a few examples of the services accessible via Interface Endpoints. You can find the full list of supported services here.
S3: Gateway vs Interface Endpoints
It's worth noting that S3 supports both Gateway and Interface endpoints. When deciding between them for Amazon S3, consider the following:
- Cost: Gateway Endpoints are free, while Interface Endpoints incur charges per hour and per GB of data transferred. Here you can find pricing information.
- Access Pattern: Gateway Endpoints are suitable for accessing S3 within the same VPC. Interface Endpoints can be used for accessing S3 from outside the VPC, including from on-premises or from different regions (Gateway Endpoints are limited to the same region).
- Bandwidth and Architecture: Interface Endpoints offer high throughput and are beneficial in centralised VPC endpoint architectures, especially when accessing S3 from multiple VPCs. Gateway Endpoints have no inherent throughput limit and are simpler to manage for in-VPC use.
- DNS Configuration: Interface Endpoints offer options for DNS configurations, allowing for more flexible connectivity setups, particularly for on-premises and cross-region access patterns. Gateway Endpoints are ideal for simple, in-VPC access to S3 at no cost, while Interface Endpoints offer more flexibility and higher throughput for more complex architectures and external VPC access.
Here you can read more about types of vpc endpoints for s3.
Conclusion
In this blog post, we have looked into of both Gateway and Interface endpoints. Rather than separating the benefits of each endpoint type, let's look at the advantages of using VPC endpoints as a whole:
-
Enhanced Security: VPC endpoints enable direct, private connectivity to AWS services, such as S3, DynamoDB, Secrets Manger, EC2 and others, reducing the need to expose traffic to the public internet and keeping your data protected.
-
Cost-effectiveness: This is especially the case (but not only!) with Gateway Endpoints, you can avoid internet egress charges, especially with high-volume data transfers. While Interface Endpoints do incur charges, they can offset these costs by reducing data transfer fees over the public internet.
-
Improved Performance and Reliability: VPC endpoints often provide lower latency and higher throughput, ensuring faster and more efficient data transfers. This increase in performance is crucial for applications requiring real-time data processing.
-
Wide Range of supported services: Interface Endpoints support a large number of AWS services, which enables secure connection with various AWS services, facilitating diverse and complex cloud architectures.
-
Compliance and Security Standards: For organisations with compliance and security requirements, VPC endpoints provide a secure communication channel, meeting various regulatory standards by keeping data within the AWS network.
-
Flexible Connectivity Options: The ability to customise DNS configurations with Interface Endpoints, as well as the simplicity of Gateway Endpoints, offers diverse connectivity options. This is beneficial for simpler in-VPC scenarios and more complex setups involving cross-region or on-premises access.
-
Simplified Network Management: VPC endpoints simplify the network architecture by reducing the need for Internet Gateways, NAT devices, or VPN connections, making network management more straightforward and less prone to security risks.
Using VPC endpoints can significantly enhance the security, performance, and efficiency of your cloud infrastructure. It can provide a robust solution for securely accessing AWS services, catering to various architectural needs and use cases.
References/further reading:





